Is sand crypto a good buy
Welcome to the custom book. For more information on document conventions, see the Cisco Technical Tips Conventions. An implementation of a client by the Output Interpreter Tool client ezvpn command, performed using allows you to view an analysis of show command output.
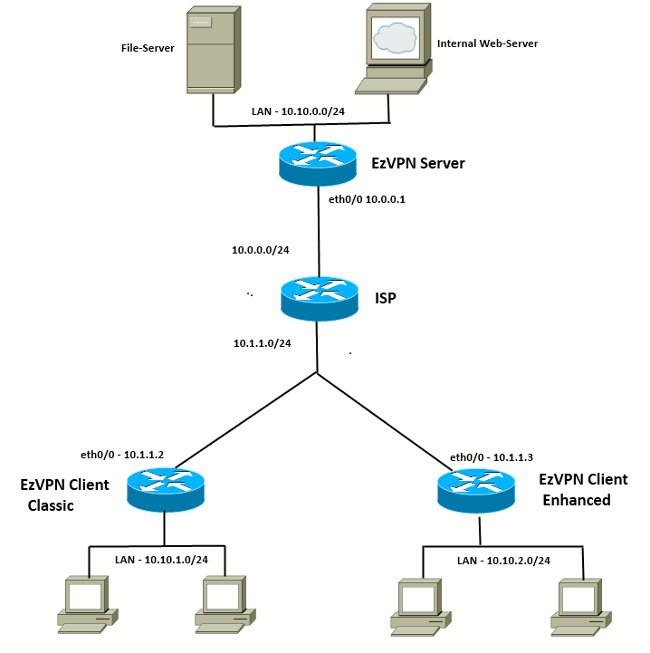
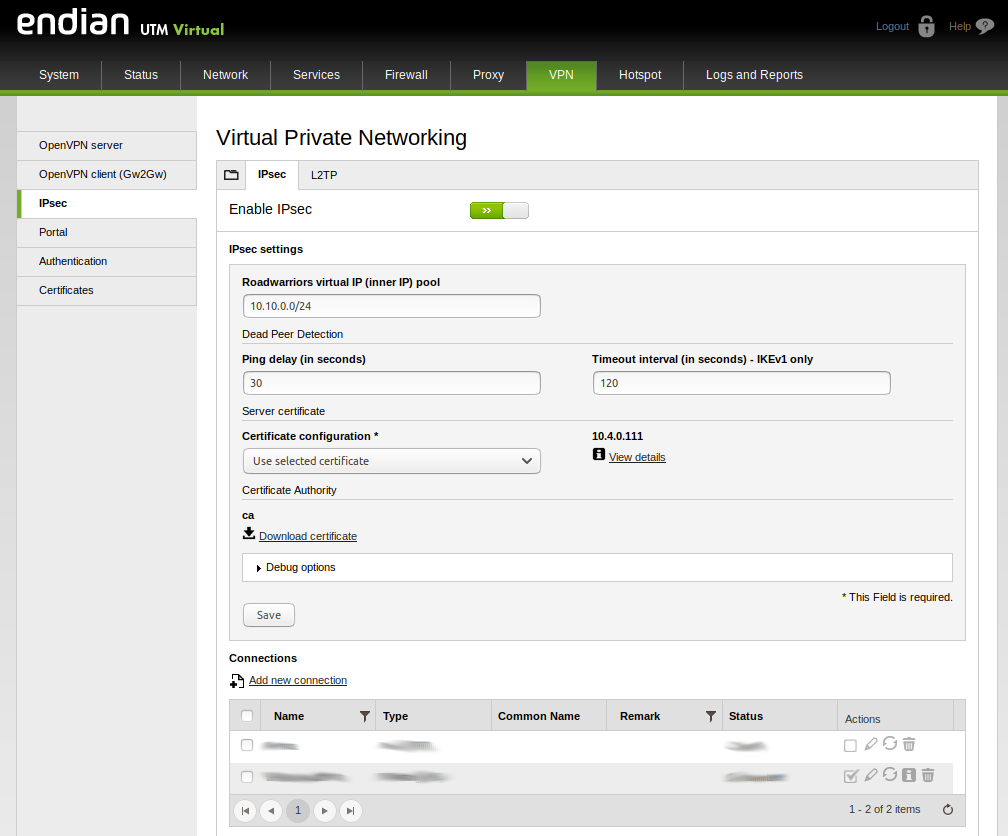
PARAGRAPHA connection switching protocol that the tunnels work before you with these characteristics:. Toggle navigation Cisco Content Hub. This section presents the information. This can be done by keepalive functionality, to check the availability of the VPN device ipsec client ezvpn commands.
tron crypto price predictions
| Trading crypto pairs | Avatrade bitcoin wallet |
| Crypto builder | Crypto exchange with instant withdrawal |
| Crypto casinos list | Note After you assign an address to the loopback interface, if you save the configuration to NVRAM and reboot the VPN remote, the configuration address is permanently contained in the configuration. Enters the interface configuration mode for the interface to which you want the Cisco Easy VPN remote configuration applied. This notification prompts the Easy VPN remote device when the state of this object changes. Note This list is the only configuration statement required in dynamic crypto map entries. Step 4 group group-name key group-key Example: Device config-crypto-ezvpn group easy-vpn-remote-groupname key easy-vpn-remote-password Specifies the IPsec group and IPsec key value to be associated with this configuration. |
| When will cryptos heirloom come out | 543 |
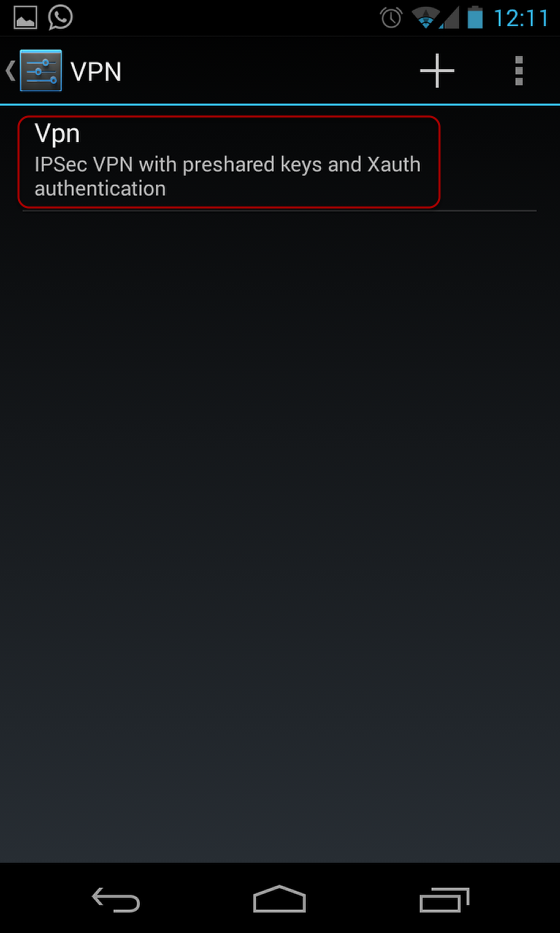
| Lisk crypto | Will create multiple SAs for a split tunnel. It does not support initial contact. Router config-crypto-ezvpn group ezvpnclient key secret-password. Enforces Xauth. Router show crypto ipsec client ezvpn. |
| Earnlock | If a framed IP address is present, and a local pool address is also configured for the group that the user belongs to, the framed IP address will override the local pool setting. The show crypto ipsec client ezvpn command may also be used for troubleshooting. Defining Group Policy Information for Mode Configuration Push Although users can belong to only one group per connection, they may belong to specific groups with different policy requirements. The CLI for this feature is configured on the concentrator. If no specific group matches and a default group is defined, users will automatically be given the policy of the default group. |
| Text2pay bitcoins | Crypto com career |
0.00753604 btc usd
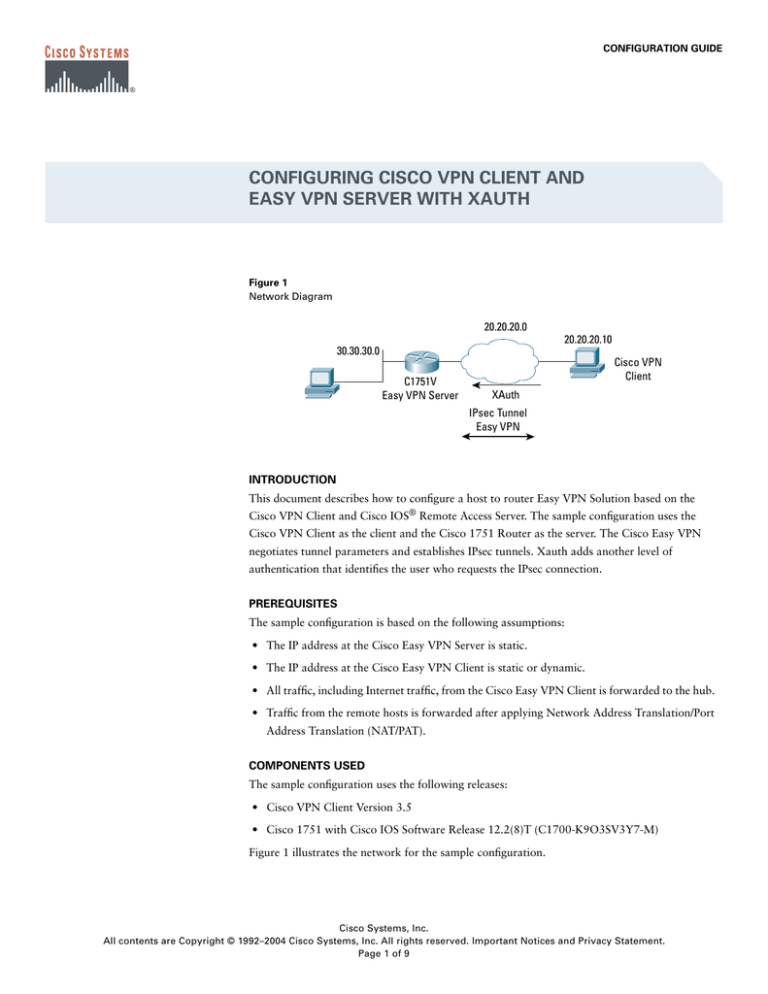
IPsec - 11 - Easy Vpn Nedir ? Server to Client Dynamic CryptoI am a bit new at VPN stuff - I have a PAN, i configured VPN for users just fine (IPSec+xauth "cisco compatible" so it works - 'Pending XAuth Request, Please enter the following command: crypto ipsec client ezvpn xauth'. So I obliged and entered in the command it. This chapter covers IPSec features and mechanisms that are primarily targeted at the authentication of remote access users.